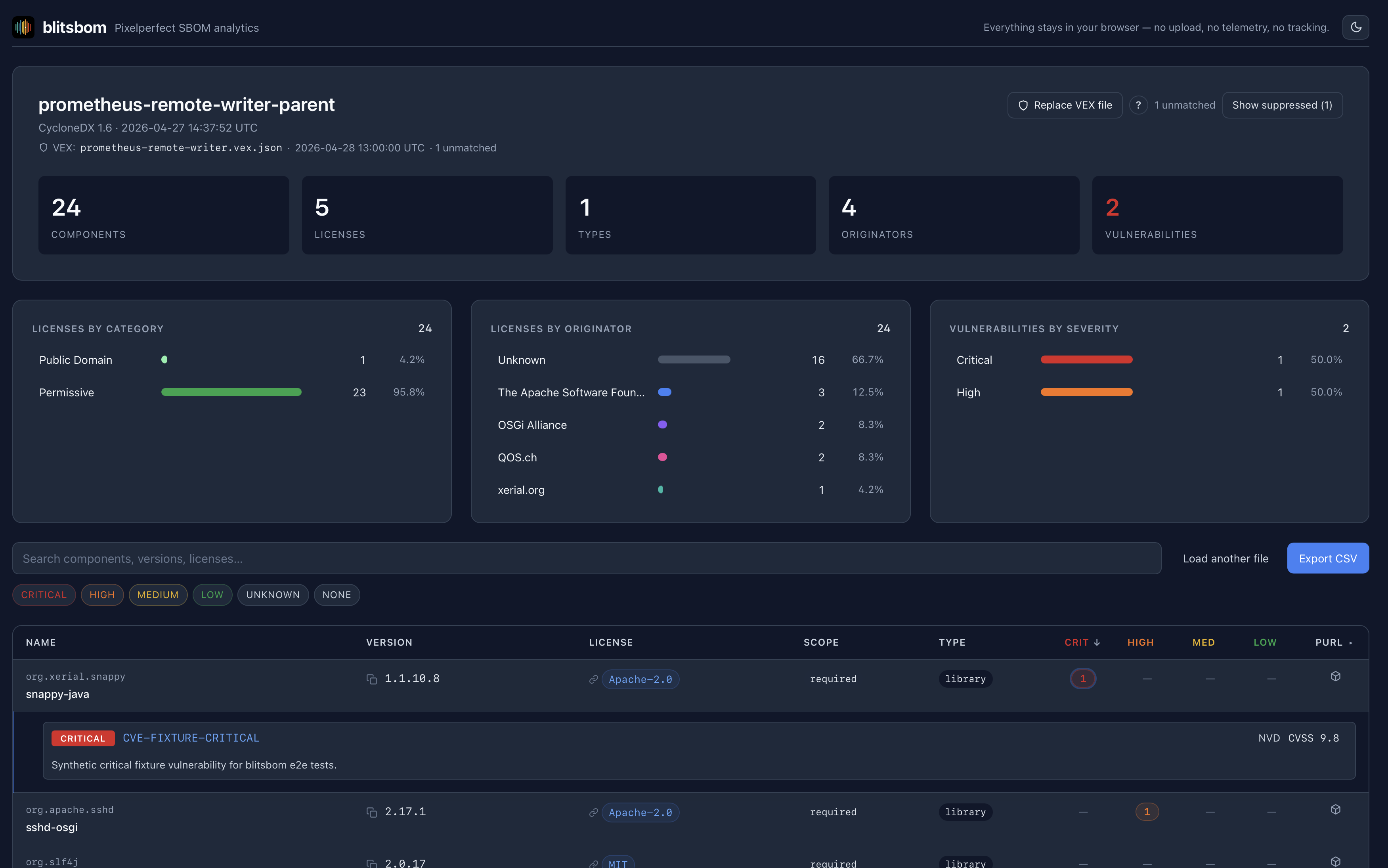
Blitsbom, browser-only SBOM viewer
I had to scratch one of my itches. I have to work with SBOMs and I couldn’t find something, so I’m announcing blitsbom — a browser-only SBOM viewer. Software Bills of Materials are everywhere now. Procurement asks for one. Compliance wants one filed. A regulator’s auditor will, at some point, want to look at one. The trouble is that the moment you actually want to read an SBOM — to skim what’s in a build, see which components are copyleft — your options are oddly bad. You either ship the file off to a SaaS scanner, install a heavyweight platform, or squint at 280,000 lines of JSON in your editor.
Continue reading